Apr 22, 2023
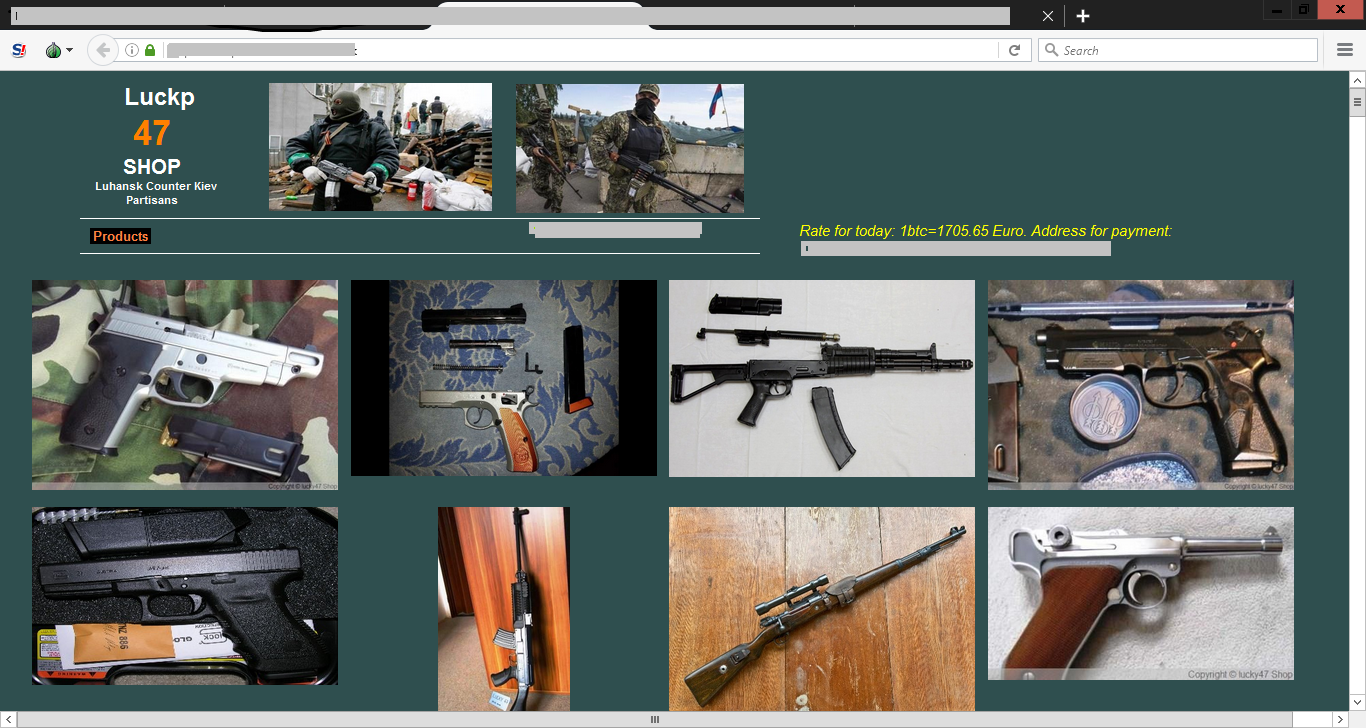
Discover the Hidden World of Dark Web Market Links

It's important to note that when accessing the dark web using Tor, your Internet Service Provider (ISP) will still be able to see that you are
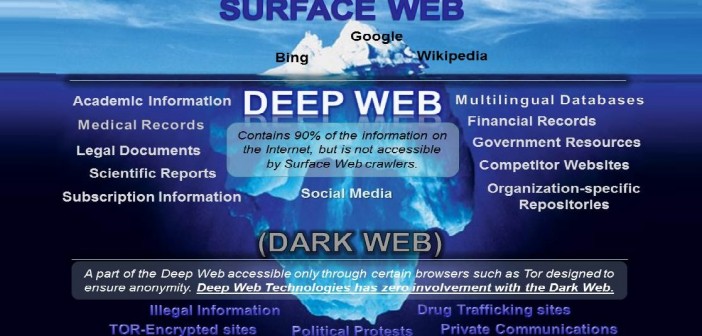
connected. This means that the quality of search results can vary greatly and a lot of the information available can be outdated. However, the technology used to create this anonymous connection is known as "onion routing," which employs multiple layers to obscure data and keep users' locations on the network hidden.
If you establish a connection to Tor after connecting to a VPN and experience an IP leak, only the IP address of the VPN will be revealed. This is an important consideration when accessing the dark web.
If you're looking to enhance your online security, you can consider accessing the dark web with the help of Tor and a VPN simultaneously. The link checker can be used to verify the status of a link. Have you ever wondered about the origin and purpose of the dark web?
Discovering the Secrets of the Dark Web: Latest Dark Web News
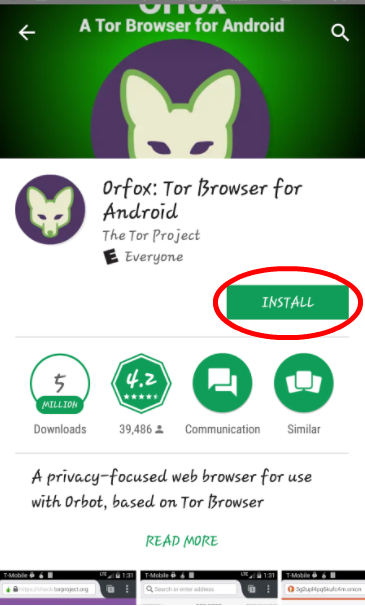
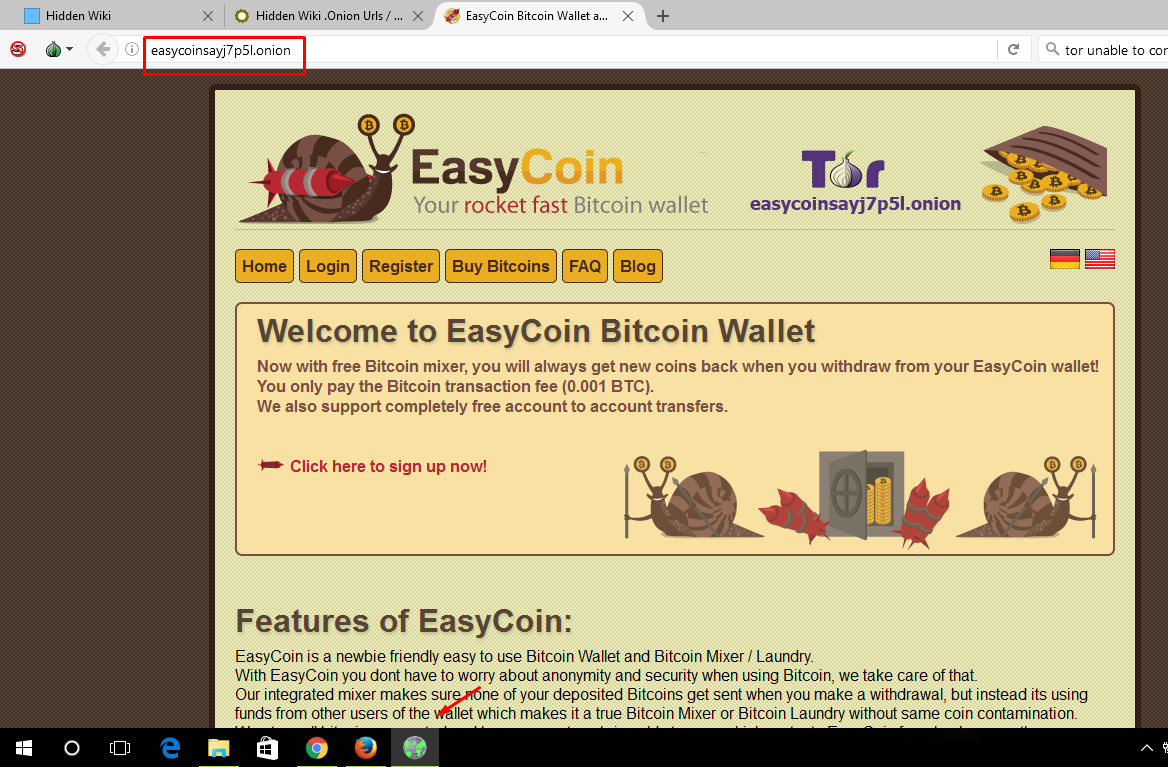
To gain entry into the dark web credit cards dark web, one must utilize the Tor network, and the ideal tool for doing this is the Tor browser. This browser is equipped with robust security features including RAM-only servers, perfect forward secrecy, an audited no-logs policy, and DNS leak protection. With these features, users can access links on the dark web with confidence and security.
Accessing the dark web allows you to explore content that isn't readily available through a simple Google search. This includes data such as iPhone app contents, Dropbox files, academic journals, court records, and private social media profiles. It's a throwback to the early days of the internet, where users had to rely on links and search fields to navigate the web. By utilizing these tools, you can browse dark web pages and discover a wealth of hidden content.
After conducting 10 trials, I consistently received precise search outcomes when accessing the dark web.
Looking to access the dark web? If you're in need of academic journals, we recommend checking out our guide on using deep web search engines for scholarly research. However, it's important to be aware of the potential dangers that come with accessing the dark web. This includes the risk of encountering DDoS attacks, botnets, and various types of malware such as remote access Trojans (RATs), keyloggers, and exploits. Additionally, there are services available on the dark web that specialize in espionage, offering customization and targeting options. For those who prioritize security, installing a virtual private network (VPN) can provide an extra layer of protection. Always proceed with caution when accessing the dark web.
Unlocking the Secrets of the Dark Web on Your iPhone
Accessing the dark web unveils a world of illegitimate content that includes black markets for illegal drugs and child pornography sites. The VPN over Tor method, while highly unlikely, can still be vulnerable to an end-to-end timing attack. For those who prioritize privacy, there are several private and encrypted email services, as well as guides on how to install anonymous operating systems and advanced tips for maintaining anonymity.
As an experienced copywriter, I can rewrite the following text on "Accessing dark web" in English. Here's my take:
One way to access the dark web is by configuring the CyberGhost VPN app to automatically connect to a preferred VPN server and launch the Tor browser app upon startup.
Unlocking the Secrets of the Dark Web with Onion Technology
Accessing the dark web can be risky as both session logs and traffic logs pose a serious threat to your privacy. It is important to note that visiting such sites may be illegal in certain jurisdictions, so it is advisable to exercise caution. To protect your privacy, avoid sharing any personal information that could identify you.
Accessing the dark web can be for various reasons, such as seeking medical advice without having to discuss personal issues with doctors in person. However, the largest source of illegal goods and services, AlphaBay, was shut down by a team of cyber cops in 2017, causing fear throughout the network. Despite this, there are concerns about the lack of WebRTC and IPv6 leak protection, which ExpressVPN offers. Nevertheless, personal tests have not shown any leaks.
Wondering why you should opt for I2P over Tor when accessing the dark web? Well, I2P offers several advantages over Tor, such as improved security and privacy, faster speeds, and the ability to host websites anonymously. With I2P, your online activity is encrypted and routed through multiple nodes, making it virtually impossible for anyone to trace your IP address or monitor your browsing activity. Additionally, I2P has a distributed network structure, which means that there is no central authority controlling the network, making it more resistant to censorship and government surveillance. So if you're looking for a more secure and private way to access the dark web, consider using I2P instead of Tor.
For Tor users located in the United States, it may be beneficial to utilize a VPN for quicker and more dependable access to the dark web. It is essential for individuals like Keepers Patrick Tiquet to stay informed about the happenings within the hacker underground, which is why he regularly checks in. The interface is user-friendly and easy to navigate, with useful explanations provided for all features and settings.
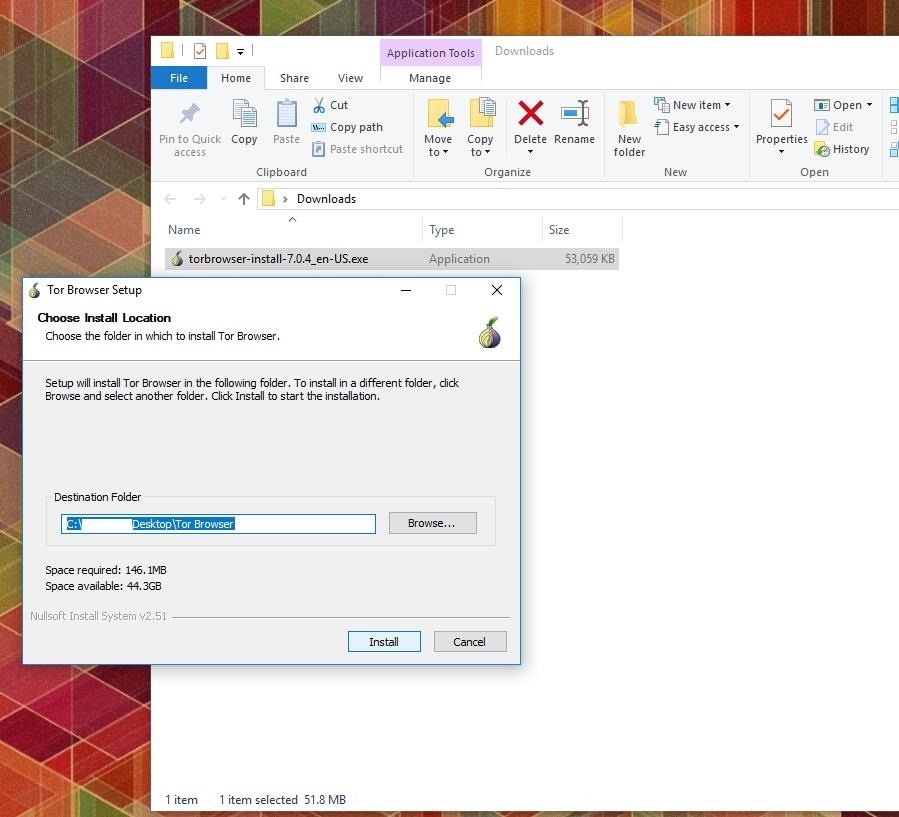
When it comes to accessing the dark web, it's important to take precautions to protect yourself and your device from potential threats. One of the key steps you can take is to use a virtual private network (VPN) like ExpressVPN, which is our top recommendation for VPNs in 2023. Additionally, it's crucial to only download the Tor Browser from the official website to avoid downloading any harmful malware, spyware, or viruses. For further protection, consider using NordVPN, which you can read more about in our comprehensive NordVPN review.
Explore further
Distributed by Фуат, LLC.